If you are searching about Logical security network perimeter security IT security plan you've visit to the right place. We have 9 Pictures about Logical security network perimeter security IT security plan like What is Cyber Range ⋅ Definition ⋅ DIATEAM, Am I prepared to respond to a Cyber Security Incident? and also Logical security network perimeter security IT security plan. Here you go:
Logical Security Network Perimeter Security IT Security Plan
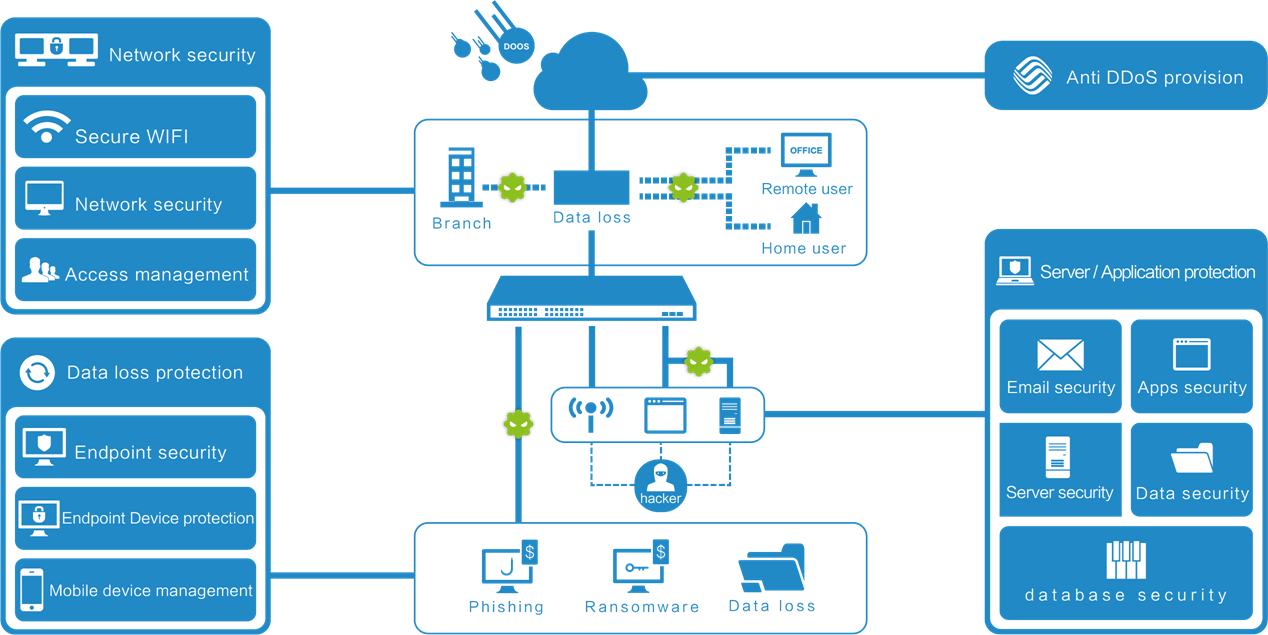 www.iicybersecurity.com
www.iicybersecurity.com security logical plan perimeter network physical implementation aspects solutions company
Am I Prepared To Respond To A Cyber Security Incident?
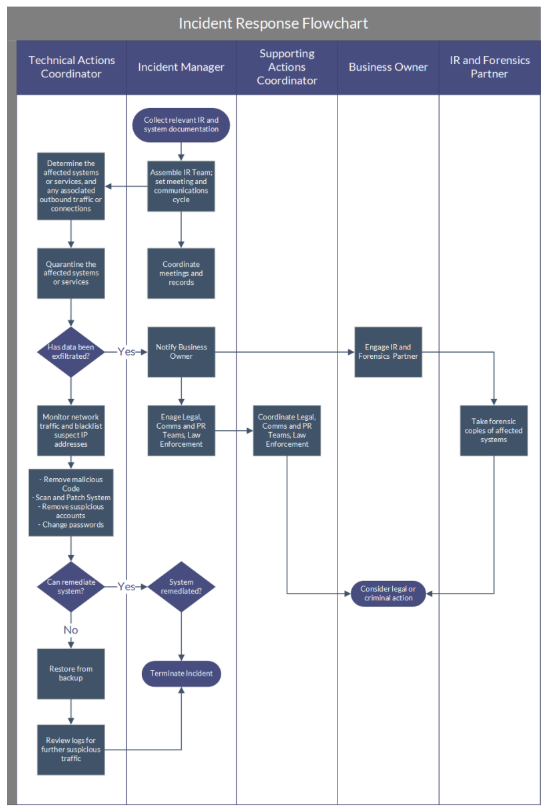 help.securitycolony.com
help.securitycolony.com security respond capability
Cyber Threat Susceptibility Assessment | Cyber Threat, Security
 www.pinterest.com
www.pinterest.com susceptibility mitre methodology tsa
What Is Cyber Range ⋅ Definition ⋅ DIATEAM
 www.diateam.net
www.diateam.net diateam
SCP - Chapter 1 - The Global Outlook For Cyber Security | AustCyber
 www.austcyber.com
www.austcyber.com security cyber global examples plan scp outlook chapter needs sector
Scikit-Learn(Cyber-security) Cheat Sheet By Sati - Download Free From
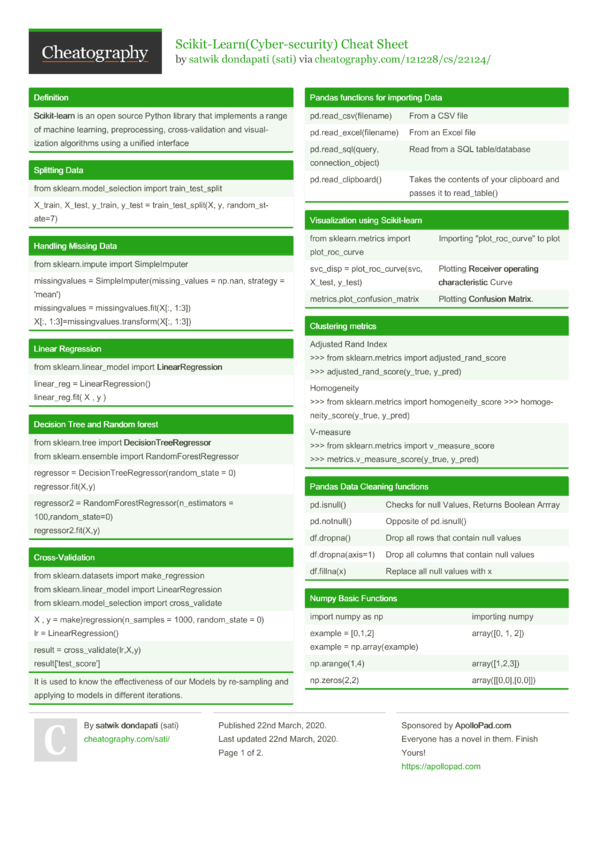 cheatography.com
cheatography.com cheat sheet cyber security learn scikit sati cheatography programming python py
 venturebeat.com
venturebeat.com Cyber Security 22-07-29=013
 www.slideshare.net
www.slideshare.net cybersecurity
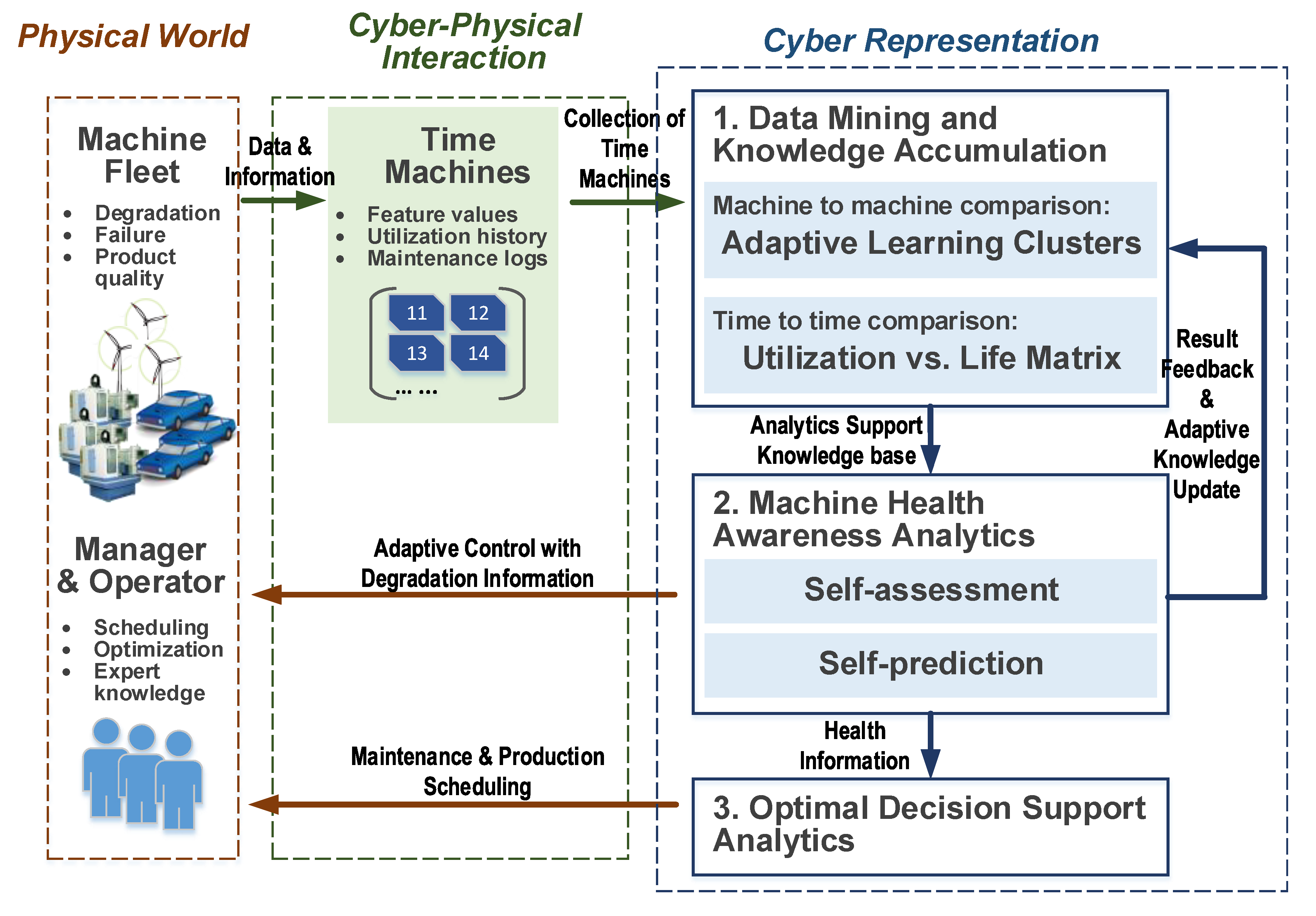
Machines | Free Full-Text | A Cyber Physical Interface For Automation
 www.mdpi.com
www.mdpi.com cyber physical systems machine interface automation examples learning machines platform methodology manufacturing mdpi capabilities analytics self figure g003
Cyber threat susceptibility assessment. Cyber physical systems machine interface automation examples learning machines platform methodology manufacturing mdpi capabilities analytics self figure g003. Logical security network perimeter security it security plan


